
Data breaches are a HIPAA nightmare in the making. Are you fully aware of your cyber risks...and of how you can help to mitigate them?
“It will never happen to me.” So say many US physicians about healthcare data breaches, a common phenomenon in today’s tech-enabled medical field. But happen it does. Just ask Sohan Dua, MD, of Northridge, California.
Several years ago, Dua, a nephrologist, received word someone broke into his practice’s computers. Since he shared an electronic health record system (EHR) with his wife, a primary-care physician, her practice had been attacked, as well. Hackers locked them out of their patient data and were demanding a hefty ransom.
It took the doctors several months to deal with the aftermath, during which neither could see patients. Fortunately, the cyber coverage in their malpractice insurance helped them remediate the damage, as well as pay for breach expenses. But even with insurance, the attacks were devastating. “We still don’t know how much money we lost,” Dua told Medical Economics. But he knows he had at least $40,000 to $50,000 in uncollected billings. “We lost patients, too,” he said.
Welcome to the frightening world of data breaches. Fifteen or 20 years ago, “cybercrime” was a foreign term to most physicians. Today, due to an explosion of external attacks and insider mistakes, physician-owners of small medical practices are now highly familiar with cybercriminals, employees and third parties improperly accessing and divulging confidential patient health information. These breaches subject them to fines and penalties for violating federal HIPAA privacy standards.
Fortunately, cybersecurity plans (and applications) are widely available, as are cyber liability insurance policies to cover the expenses that follow a data breach.
The scope of the issue
Data security is an immense problem, say industry experts. In 2019, healthcare suffered a “staggering number of reported hacking incidents,” says Protenus, Inc., a compliance analytics firm. According to its 2020 Breach Barometer, 572 data breaches were reported in 2019 to the U.S. Department of Health and Human Services (HHS), the media or another source. In the 481 incidents for which it had data, Protenus said 41.4 million patient records were affected. The 2019 cases were a sharp increase over 2018, when the firm identified 503 incidents and 27.3 million affected patient records.
Protenus adds that its 2019 data likely understates actual results since it lacks data for two large incidents that occurred in 2019, including one affecting 500 dental practices and clinics. Of the 12 largest healthcare data breaches in 2019, eight involved insider errors and nine involved hacking. One piece of good news was that insider-related incidents declined from 139 in 2018 to 110 in 2019. However, the number of involved patient records jumped to 3.8 million in 2019 from 2.8 million in 2018.
The Protenus findings track with Verizon’s 2020 Data Breach Incident Report, which revealed 796 2019 data breach incidents, 521 of which had confirmed data disclosures. The 521 confirmed incidents compared with 304 incidents in Verizon’s prior report.
However, the frequency of healthcare data breaches is only one part of the story. The other is their financial impact. According to a Ponemon Institute study, data breaches cost the industry $6.2 billion in 2016, a number likely to be much higher today. The study also found that roughly 90 percent of healthcare organizations experienced a cyber incident in the prior two years. About half (45 percent) of the organizations surveyed had more than five data breaches.
When the focus shifts to the data breach cost per patient record, the picture becomes even more alarming. In a 2018 study, Ponemon found that healthcare data breach costs averaged $408 per record. This was the highest amount for any industry and about 300 percent higher than the all-industry average of $148. Which raises the question: If your entire patient database were stolen, could you afford the financial impact?
The scope and severity of data breaches, as evidenced in the above studies, poses three other questions to physicians operating small medical offices today:
- Are you prepared to deal with the HIPAA implications of a data breach?
- Do you understand the full scope of the cyber risks your medical practice faces?
- Are you aware of how cyber liability insurance can help mitigate your financial losses after an incident?
Let’s consider each question in turn.
HIPAA Implications
The Health Insurance Portability and Accountability Act (HIPAA) is a federal law familiar to all medical practice owners. Its purpose is to establish privacy standards to safeguard patients’ medical records and other personal health information. HIPAA applies to nearly every business, or related entity, in the healthcare sector and their business partners.
Although a full HIPAA discussion is beyond the scope of this article, it’s important to be familiar with the full suite of HIPAA regulations, including:
- The Privacy Rule, which assures the privacy of individually identifiable health data.
- The Security Rule, which provides national standards to safeguard Electronic Protected Health Information (EPHI).
- The Breach Notification Rule, which requires covered entities (CEs) and business associates (BAs) to notify HHS after a data breach occurs.
The goal is to avoid a HIPAA violation. Common violations that lead to data breaches include:
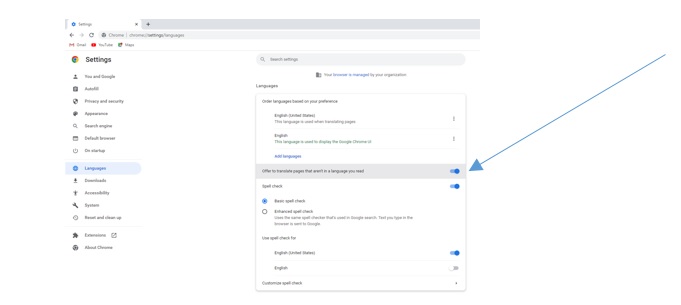
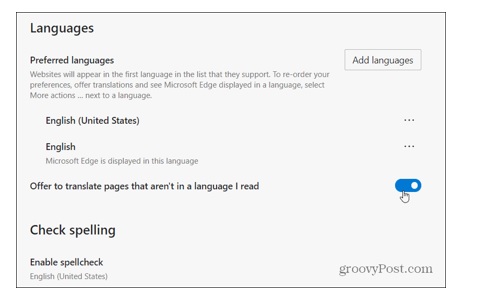
- Not installing software patches for software such as EHRs, Java, Flash, Microsoft Office products, and your computer operating systems (Windows and Mac OS).
- Not maintaining HIPAA-compliant firewalls (home or Internet service provider firewalls are not HIPAA compliant).
- Not installing intrusion prevention applications for an extra level of protection against hackers.
- Not updating your anti-virus applications.
- Not encrypting your PHI, including when data is in transit or stationary and for mobile devices such as laptops, tablets, smartphones and USB drives.
- Not installing contemporary wireless encryption standards—Advanced Encryption Standard (AES), not the older WEP standard.
- Inappropriately publishing or sharing a patient’s personal data.
- Sharing information with an unauthorized person.
- Losing or failing to secure devices that contain confidential personal data.
- Sharing computer logins with someone in the office who lacks appropriate access privileges.
- Not properly disposing of PHI.
- Not maintaining required HIPAA documentation and doing risk assessments.
Avoiding these mistakes and others will help you prevent a HIPAA data-breach violation. However, if cyber misfortune strikes your practice, you must report the incident to the HHS Office for Civil Rights (OCR). The OCR will then investigate your case if it involves more than 500 patients. It will also publish details of incidents that occurred within the last two years on its online “Wall of Shame.”
Being publicly shamed is bad enough. Even worse is getting fined. If OCR finds you negligent, you might face penalties of up to $50,000 per incident. What’s more, state attorneys general might pursue legal action against you. Finally, the U.S Department of Justice might file criminal penalties against you for knowingly misusing unique health identifiers or improperly acquiring or disclosing protected health information (PHI). This much is clear: avoiding a data breach is a much better strategy than dealing with its HIPAA aftermath.
Scope of Risks
In thinking about your practice’s many cyber risks, you might be wondering, “Why me?” In other words, why are hackers coming out of the network to steal your data? The answer is complex:
- First, medical records are a valuable commodity on the Internet black market. They include copious patient data such as Social Security numbers, birth dates and home addresses. Stolen data help criminals create phony accounts in your (and your patients’) names and access related financial accounts. Because of this utility, hackers can sell a patient’s medical data for 10 to 20 times the going rate of stolen credit card numbers.
- Second, medical practices until recently were part of a cottage industry that lacked the funds and technical prowess to mount strong cyber defenses. Result: hackers targeted medical offices because they found them relatively easy to victimize.
- Third, as the healthcare industry increasingly deploys medical devices connected to the Internet (Internet of Things), criminals have countless new attack vectors to pursue.
Whatever the reason, if you’re not careful, criminals can steal the data that federal authorities require you to safeguard, exposing you to large financial and legal penalties. However, even though the majority of healthcare data breaches involve criminals, a significant portion results from insider acts, both innocent and malicious.
How broad are the cyber risks your practice faces? About as broad as the morbidity and mortality risks a human being faces. Here are some of the major ones, according to Consolidated Technologies, Inc., a healthcare communications and IT managed services provider.
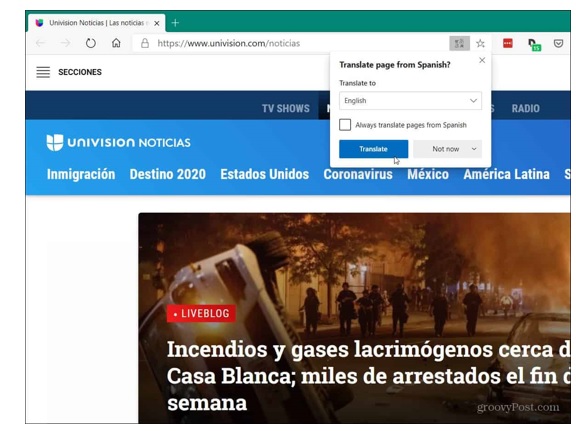
- Malware and phishing. These are schemes that plant malevolent scripts on an individual computer or steal login credentials. A common approach: send an email that mimics one from a legitimate company, requesting login information for your network, which the hacker then uses to penetrate your network. Another is tricking employees into clicking on an email link. This installs a malware script that prevents you from accessing your applications and data. Known as ransomware, this approach can literally shut down your practice indefinitely until you reload your backup data or pay the ransom. According to a Comparitech study, 172 healthcare organizations have suffered ransomware attacks since 2016, costing the industry some $150 million.
- Vendors. Companies that have physical access to your office might be able to gain access to your computers and patient data if they have technical savvy. Or companies with whom you do business (example: medical transcribers) might get hacked, giving criminals an entry path to your data. Or an IT vendor might make a coding error that leaves your system vulnerable to external attack or might access your data, but fail to safeguard it as well as you would. The possibilities are endless.
- Software supply chains. Hackers may use a supply-side-chain attack to gain entry into a system they otherwise can’t penetrate or to use a major healthcare vendor to target the entire industry. One technique is to hijack a supplier’s domain and redirect traffic to an infected domain.
- Staff. Employees who are authorized to view patient data may decide to engage in identity theft or use sensitive information to blackmail patients. More commonly, they will make a mistake that gives a malicious actor access to your patient information. An IBM study found that employee errors triggered 95 percent of data breaches.
- Unsecured mobile devices. Medical practices that allow smartphone logins may not require the devices to meet current security standards. This means a patient using a sub-standard device can defeat what you thought were robust defenses.
- Lost and stolen mobile devices. Most people have lost their mobile phones at least once in their lives. When this happens and the phone falls into malicious hands, it can be used to access patient data using old or stored login data.
- Unrestricted access to computers. Computers that members of the public can easily access can be used to access confidential patient data. Alternatively, phishing targeted at general-access computers might open a gateway for criminals to penetrate more sensitive areas of your network.
- Improper disposal of old hardware. Criminals can use any discarded mobile device or piece of computer hardware you’ve used to access EHRs to access your network and steal data. Deleting files or even reformatting hard drives might not be sufficient protection.
In short, the risks just mentioned can produce a perfect storm of headaches for your medical practice: loss of confidential client data; theft of proprietary business information; harm to crucial computer systems, applications, and databases; loss of employee records; disruption of supply chains and vendor accounts; inability to bill for services rendered and a threat to the continuity of patient care.
With so many potentially catastrophic risks, it’s crucial to mitigate them with a robust cybersecurity plan and with cyber liability insurance. Start by identifying your major cyber risks and then create plans to defend your practice and to respond to a breach should one occur. There are resources available on the Internet to help you accomplish these tasks.
Buying cyber liability insurance is another crucial step. A form of insurance that covers data breach costs, it also provides technical resources to help you prevent and/or recover from an incident. Although medical malpractice insurance may provide some protection against data breaches, dedicated cyber liability policies provide more robust coverage. In today’s risky environment, a comprehensive cyber liability policy is the gold standard most physician-practice owners should consider buying.
How does cyber liability insurance work? It provides two levels of protection: first party and third party.
First-party protection means the policy helps you mitigate a breach’s negative impact on your practice. It does this by paying for things like:
- Investigation: hiring a forensics IT expert to determine how the breach happened and to fix the security hole.
- Ransoms: meeting a cybercriminal’s payment demand to unlock your computers, especially if you lack a current system backup.
- HIPAA fines: providing funds to cover HIPAA penalties or fines that result from the incident.
- Public relations: hiring a PR or crisis management firm to help stem customer defections after a data breach.
- Patient credit monitoring: providing credit monitoring to all patients involved in the incident.
- Notification expenses: letting your patients know their personal data was released in a data breach.
- Legal advice: retaining an attorney to counsel you on the legal impact of the attack.
- Business interruption support: providing cash to replace income lost due to your inability to work after the cyber breach.
Third-party protection means the policy helps you deal with third-party litigation. Your policy will provide funds to retain an attorney to defend you and to pay for legal settlements and judgments imposed on you if you’re found to be negligent.
Put first-party and third-party coverage together and what do you have? A robust safety net to address most cyber-related risks. However, be aware that this form of insurance covers your computer data, not your hardware. Your commercial property insurance or business owner’s policy will cover physical damage to your computer equipment.
360 Coverage Pros offers top-rated insurance solutions for many forms of business insurance, and we stand ready to assist healthcare professionals in mitigating their data breach risks with comprehensive and affordable cyber liability insurance. To review policy features, benefits and cost please visit https://www.360coveragepros.com/cyber-liability.


Share this page.